MANAGING DMARC REQUIREMENTS WITH FORCEPOINT EMAIL SECURITY
The Department of Homeland Security (DHS) continues to push agencies to accelerate the modernization of federal government systems and networks.
In 2014 Congress passed the Federal Information Security Modernization Act (FISMA) with the intent of implementing specific security standards that have been widely adopted in commercial industries so that federal agencies can secure mission-critical data and systems. DHS develops and oversees the implementation of binding operational directives (BODs) pursuant to FISMA. Federal agencies are required to comply with these DHS-developed directives.
Based on “recent network scan data and a clear potential for harm” DHS issued BOD-18-01 on October 16th, 2017. The directive calls for agencies to submit an action plan to enhance web and email security and specifically requires the strengthening of email authentication policies.
Email Authentication with DMARC
Agencies have until November 15th, 2017 to submit a plan for implementing Domain-based Message Authentication, Reporting and Conformance (DMARC), an email authentication policy and reporting protocol designed to detect and prevent email spoofing. Organizations using DMARC can specify what happens to unauthenticated inbound messages: they can be monitored but still delivered to the recipient’s inbox (allow), they can be moved to the spam or junk folder (quarantine), or their delivery can be blocked completely (reject).
At a minimum, agencies must implement a DMARC policy that is set to “allow” by January 14th, and at least one address must be configured to receive aggregate and/or failure reports. Within one year, the DMARC policy must be set to “reject” all unauthenticated inbound emails.
As of August 1st 2017, only 135 federal email domains out of 1,315 — just 10 percent — had some form of the DMARC protocol deployed, according to the non-profit Global Cyber Alliance. Moreover, most of the sites that have actually deployed the protocol have yet to enable the functionality.
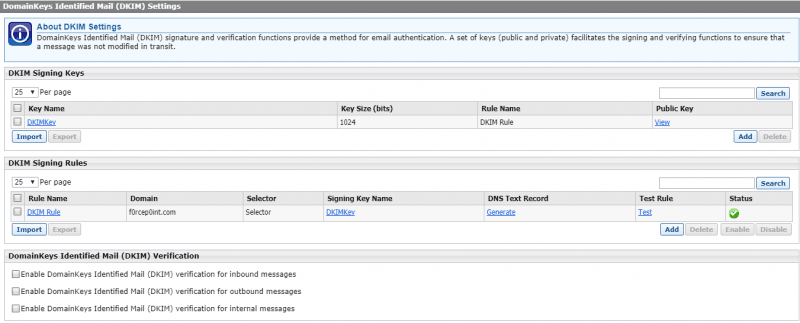
In the same timeframe, DHS is requiring all second-level agency domains to have valid DomainKeys Identified Mail (DKIM) records, which allow organizations to validate a domain name identity that is associated with a message through cryptographic authentication.
Managing the DMARC Requirement with Forcepoint Email Security
Forcepoint Email Security is an email gateway solution that allows our customers to quickly and seamlessly meet the DMARC requirements within BOD-18-01 out of the box. Forcepoint Email Security has the ability to check all inbound email for DMARC validation, and policies can easily be set to “allow”, “quarantine” or “reject”. DMARC aggregate and failure reports for inbound emails are generated and available for compliance with BOD-18-01. Forcepoint Email Security also manages all DKIM signing for outbound email messages for full compliance with DMARC standards.